How To and technical articles, covering a range of subjects relating to computers, operating system configuration and day-to-day computer use.
Looking for something specific? Try the search box.
How to Extend The Life of Windows 10 Beyond Its End-of-life Date With Micropatching!
Extend the life of Windows 10 beyond its End of Life Date using the groundbreaking technology of Micropatching.
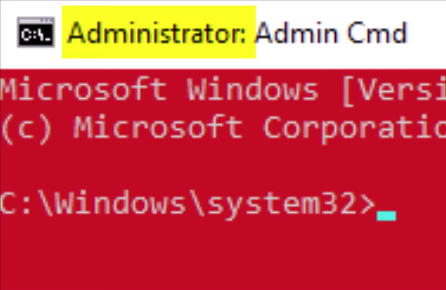
Read MoreHow to make a 1 click Windows shortcut command prompt, with admin rights.
How to make a 1 click Windows shortcut command prompt, with admin rights.
Read MoreWant to speed up your slow Windows PC? See these 10 Quick Tips
Is your Windows PC starting to drag its feet? Here are ten effective tips to help give your machine a speed boost and enhance your overall computing experience.
Read MoreUbuntu vs Mint Linux. Which Should You Choose?
Are you diving into the Linux world and torn between Ubuntu and Mint? Let’s break it down!
Read MoreWhat to Expect from Microsoft Windows 12
Windows 12 is expected to introduce a more streamlined and intuitive user interface. With a focus on modern design principles, users can anticipate a cleaner look with updated icons, more dynamic themes, and improved customization options.
Read MorePreparing for the End of Windows 10 Support. Options, Solutions And Pitfalls!
As you are probably aware, Microsoft’s support for Windows 10 ends on October 14, 2025. So, now is a good time to consider your options for maintaining a secure and functional computing environment.
Read MoreTop 5, FREE Essential Windows Software
Everyone loves free software. Check out my latest video featuring my Top 5 picks for free Essential Windows Software.
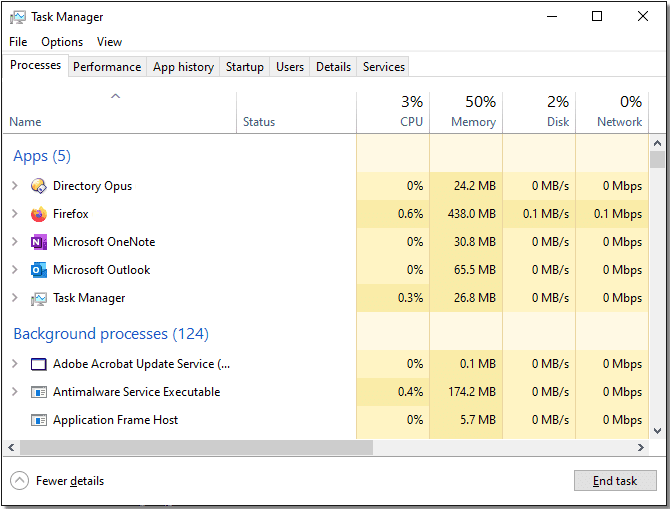
Read MoreThe Easiest And Fastest Way To Launch The Task Manager In Windows 10/11
When your PC is running slowly, the fewer keystrokes you need in order to display the Windows Task Manager, the better. This Quick Bytes video shows you how, in under one minute.
Read More